Table of Contents
- Features and Benefits
- File System Access Controls
- Share Definition Access Controls
- Access Controls on Shares
- MS Windows Access Control Lists and UNIX Interoperability
- Managing UNIX Permissions Using NT Security Dialogs
- Viewing File Security on a Samba Share
- Viewing File Ownership
- Viewing File or Directory Permissions
- Modifying File or Directory Permissions
- Interaction with the Standard Samba “create mask” Parameters
- Interaction with the Standard Samba File Attribute Mapping
- Windows NT/200X ACLs and POSIX ACLs Limitations
- Common Errors
Advanced MS Windows users are frequently perplexed when file, directory, and share manipulation of resources shared via Samba do not behave in the manner they might expect. MS Windows network administrators are often confused regarding network access controls and how to provide users with the access they need while protecting resources from unauthorized access.
Many UNIX administrators are unfamiliar with the MS Windows environment and in particular have difficulty in visualizing what the MS Windows user wishes to achieve in attempts to set file and directory access permissions.
The problem lies in the differences in how file and directory permissions and controls work between the two environments. This difference is one that Samba cannot completely hide, even though it does try to bridge the chasm to a degree.
POSIX Access Control List technology has been available (along with extended attributes) for UNIX for many years, yet there is little evidence today of any significant use. This explains to some extent the slow adoption of ACLs into commercial Linux products. MS Windows administrators are astounded at this, given that ACLs were a foundational capability of the now decade-old MS Windows NT operating system.
The purpose of this chapter is to present each of the points of control that are possible with Samba-3 in the hope that this will help the network administrator to find the optimum method for delivering the best environment for MS Windows desktop users.
This is an opportune point to mention that Samba was created to provide a means of interoperability and interchange of data between differing operating environments. Samba has no intent to change UNIX/Linux into a platform like MS Windows. Instead the purpose was and is to provide a sufficient level of exchange of data between the two environments. What is available today extends well beyond early plans and expectations, yet the gap continues to shrink.
Samba offers much flexibility in file system access management. These are the key access control facilities present in Samba today:
Samba Access Control Facilities
UNIX File and Directory Permissions
Samba honors and implements UNIX file system access controls. Users who access a Samba server will do so as a particular MS Windows user. This information is passed to the Samba server as part of the logon or connection setup process. Samba uses this user identity to validate whether or not the user should be given access to file system resources (files and directories). This chapter provides an overview for those to whom the UNIX permissions and controls are a little strange or unknown.
Samba Share Definitions
In configuring share settings and controls in the
smb.conffile, the network administrator can exercise overrides to native file system permissions and behaviors. This can be handy and convenient to effect behavior that is more like what MS Windows NT users expect, but it is seldom the best way to achieve this. The basic options and techniques are described herein.Just as it is possible in MS Windows NT to set ACLs on shares themselves, so it is possible to do in Samba. Few people make use of this facility, yet it remains one of the easiest ways to affect access controls (restrictions) and can often do so with minimum invasiveness compared with other methods.
MS Windows ACLs through UNIX POSIX ACLs
The use of POSIX ACLs on UNIX/Linux is possible only if the underlying operating system supports them. If not, then this option will not be available to you. Current UNIX technology platforms have native support for POSIX ACLs. There are patches for the Linux kernel that also provide this support. Sadly, few Linux platforms ship today with native ACLs and extended attributes enabled. This chapter has pertinent information for users of platforms that support them.
Perhaps the most important recognition to be made is the simple fact that MS Windows NT4/200x/XP implement a totally divergent file system technology from what is provided in the UNIX operating system environment. First we consider what the most significant differences are, then we look at how Samba helps to bridge the differences.
Samba operates on top of the UNIX file system. This means it is subject to UNIX file system conventions and permissions. It also means that if the MS Windows networking environment requires file system behavior, that differs from UNIX file system behavior then somehow Samba is responsible for emulating that in a transparent and consistent manner.
It is good news that Samba does this to a large extent, and on top of that, provides a high degree
of optional configuration to override the default behavior. We look at some of these overrides,
but for the greater part we stay within the bounds of default behavior. Those wishing to explore
the depths of control ability should review the smb.conf man page.
The following compares file system features for UNIX with those of MS Windows NT/200x:
- Name Space
MS Windows NT4/200x/XP file names may be up to 254 characters long, and UNIX file names may be 1023 characters long. In MS Windows, file extensions indicate particular file types; in UNIX this is not so rigorously observed because all names are considered arbitrary.
What MS Windows calls a folder, UNIX calls a directory.
- Case Sensitivity
MS Windows file names are generally uppercase if made up of 8.3 (8-character file name and 3 character extension. File names that are longer than 8.3 are case preserving and case insensitive.
UNIX file and directory names are case sensitive and case preserving. Samba implements the MS Windows file name behavior, but it does so as a user application. The UNIX file system provides no mechanism to perform case-insensitive file name lookups. MS Windows does this by default. This means that Samba has to carry the processing overhead to provide features that are not native to the UNIX operating system environment.
Consider the following. All are unique UNIX names but one single MS Windows file name:
MYFILE.TXT MyFile.txt myfile.txt
So clearly, in an MS Windows file namespace these three files cannot co-exist, but in UNIX they can.
So what should Samba do if all three are present? That which is lexically first will be accessible to MS Windows users; the others are invisible and unaccessible any other solution would be suicidal. The Windows client will ask for a case-insensitive file lookup, and that is the reason for which Samba must offer a consistent selection in the event that the UNIX directory contains multiple files that would match a case insensitive file listing.
- Directory Separators
MS Windows and DOS use the backslash
\as a directory delimiter, and UNIX uses the forward-slash/as its directory delimiter. This is handled transparently by Samba.- Drive Identification
MS Windows products support a notion of drive letters, like
C:, to represent disk partitions. UNIX has no concept of separate identifiers for file partitions; each such file system is mounted to become part of the overall directory tree. The UNIX directory tree begins at/just as the root of a DOS drive is specified asC:\.- File Naming Conventions
MS Windows generally never experiences file names that begin with a dot (
.), while in UNIX these are commonly found in a user's home directory. Files that begin with a dot (.) are typically startup files for various UNIX applications, or they may be files that contain startup configuration data.- Links and Short-Cuts
MS Windows make use of links and shortcuts that are actually special types of files that will redirect an attempt to execute the file to the real location of the file. UNIX knows of file and directory links, but they are entirely different from what MS Windows users are used to.
Symbolic links are files in UNIX that contain the actual location of the data (file or directory). An operation (like read or write) will operate directly on the file referenced. Symbolic links are also referred to as “soft links.” A hard link is something that MS Windows is not familiar with. It allows one physical file to be known simultaneously by more than one file name.
There are many other subtle differences that may cause the MS Windows administrator some temporary discomfort in the process of becoming familiar with UNIX/Linux. These are best left for a text that is dedicated to the purpose of UNIX/Linux training and education.
There are three basic operations for managing directories: create, delete,
rename. Managing Directories with UNIX and
Windows compares the commands in Windows and UNIX that implement these operations.
Table 16.1. Managing Directories with UNIX and Windows
| Action | MS Windows Command | UNIX Command |
|---|---|---|
| create | md folder | mkdir folder |
| delete | rd folder | rmdir folder |
| rename | rename oldname newname | mv oldname newname |
The network administrator is strongly advised to read basic UNIX training manuals and reference materials regarding file and directory permissions maintenance. Much can be achieved with the basic UNIX permissions without having to resort to more complex facilities like POSIX ACLs or extended attributes (EAs).
UNIX/Linux file and directory access permissions involves setting three primary sets of data and one control set. A UNIX file listing looks as follows:
$ls -latotal 632 drwxr-xr-x 13 maryo gnomes 816 2003-05-12 22:56 . drwxrwxr-x 37 maryo gnomes 3800 2003-05-12 22:29 .. dr-xr-xr-x 2 maryo gnomes 48 2003-05-12 22:29 muchado02 drwxrwxrwx 2 maryo gnomes 48 2003-05-12 22:29 muchado03 drw-rw-rw- 2 maryo gnomes 48 2003-05-12 22:29 muchado04 d-w--w--w- 2 maryo gnomes 48 2003-05-12 22:29 muchado05 dr--r--r-- 2 maryo gnomes 48 2003-05-12 22:29 muchado06 drwsrwsrwx 2 maryo gnomes 48 2003-05-12 22:29 muchado08 ---------- 1 maryo gnomes 1242 2003-05-12 22:31 mydata00.lst --w--w--w- 1 maryo gnomes 7754 2003-05-12 22:33 mydata02.lst -r--r--r-- 1 maryo gnomes 21017 2003-05-12 22:32 mydata04.lst -rw-rw-rw- 1 maryo gnomes 41105 2003-05-12 22:32 mydata06.lst$
The columns represent (from left to right) permissions, number of hard links to file, owner, group, size (bytes), access date, time of last modification, and file name.
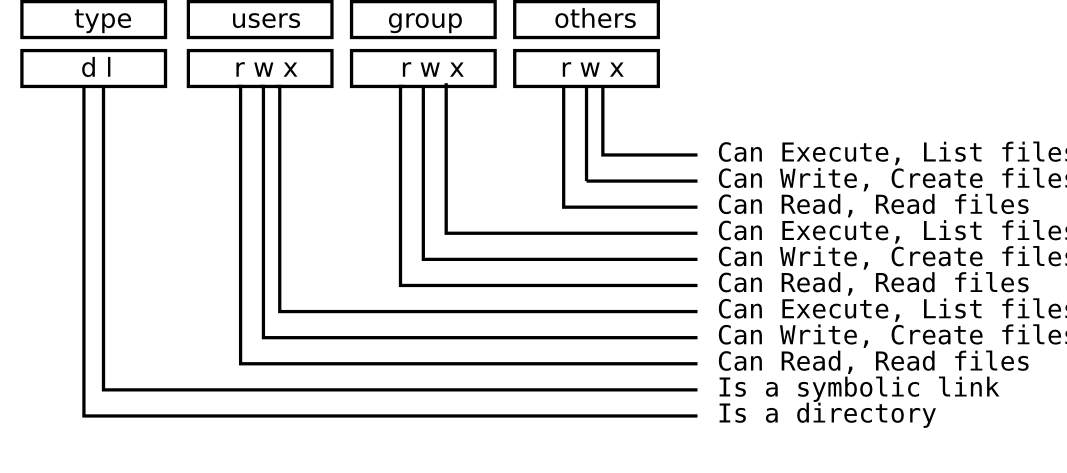
An overview of the permissions field is shown in Overview of UNIX permissions field.
Any bit flag may be unset. An unset bit flag is the equivalent of "cannot" and is represented as a “-” character (see “Example File”)
Example 16.1. Example File
-rwxr-x--- Means:
^^^ The owner (user) can read, write, execute
^^^ the group can read and execute
^^^ everyone else cannot do anything with it.
Additional possibilities in the [type] field are c = character device, b = block device, p = pipe device, s = UNIX Domain Socket.
The letters rwxXst set permissions for the user, group, and others as read (r), write (w),
execute (or access for directories) (x), execute only if the file is a directory or already has execute
permission for some user (X), set user (SUID) or group ID (SGID) on execution (s), sticky (t).
When the sticky bit is set on a directory, files in that directory may be unlinked (deleted) or renamed only by root or their owner.
Without the sticky bit, anyone able to write to the directory can delete or rename files. The sticky bit is commonly found on
directories, such as /tmp, that are world-writable.
When the set user or group ID bit (s) is set on a directory, then all files created within it will be owned by the user and/or group whose `set user or group' bit is set. This can be helpful in setting up directories for which it is desired that all users who are in a group should be able to write to and read from a file, particularly when it is undesirable for that file to be exclusively owned by a user whose primary group is not the group that all such users belong to.
When a directory is set d-wx--x---, the owner can read and create (write) files in it, but because
the (r) read flags are not set, files cannot be listed (seen) in the directory by anyone. The group can read files in the
directory but cannot create new files. If files in the directory are set to be readable and writable for the group, then
group members will be able to write to (or delete) them.
People have asked on the Samba mailing list how is it possible to protect files or directories from deletion by users. For example, Windows NT/2K/XP provides the capacity to set access controls on a directory into which people can write files but not delete them. It is possible to set an ACL on a Windows file that permits the file to be written to but not deleted. Such concepts are foreign to the UNIX operating system file space. Within the UNIX file system anyone who has the ability to create a file can write to it. Anyone who has write permission on the directory that contains a file and has write permission for it has the capability to delete it.
For the record, in the UNIX environment the ability to delete a file is controlled by the permissions on the directory that the file is in. In other words, a user can delete a file in a directory to which that user has write access, even if that user does not own the file.
Of necessity, Samba is subject to the file system semantics of the host operating system. Samba is therefore limited in the file system capabilities that can be made available through Windows ACLs, and therefore performs a "best fit" translation to POSIX ACLs. Some UNIX file systems do, however support, a feature known as extended attributes. Only the Windows concept of inheritance is implemented by Samba through the appropriate extended attribute.
The specific semantics of the extended attributes are not consistent across UNIX and UNIX-like systems such as Linux.
For example, it is possible on some implementations of the extended attributes to set a flag that prevents the directory
or file from being deleted. The extended attribute that may achieve this is called the immutible bit.
Unfortunately, the implementation of the immutible flag is NOT consistent with published documentation. For example, the
man page for the chattr on SUSE Linux 9.2 says:
A file with the i attribute cannot be modified: it cannot be deleted or renamed, no link can be created to this file and no data can be written to the file. Only the superuser or a process possessing the CAP_LINUX_IMMUTABLE capability can set or clear this attribute.
A simple test can be done to check if the immutible flag is supported on files in the file system of the Samba host server.
Procedure 16.1. Test for File Immutibility Support
Create a file called
filename.Login as the
rootuser, then set the immutibile flag on a test file as follows:root#chattr +i `filename'Login as the user who owns the file (not root) and attempt to remove the file as follows:
mystic:/home/hannibal > rm filename
It will not be possible to delete the file if the immutible flag is correctly honored.
On operating systems and file system types that support the immutible bit, it is possible to create directories that cannot be deleted. Check the man page on your particular host system to determine whether or not immutable directories are writable. If they are not, then the entire directory and its contents will effectively be protected from writing (file creation also) and deletion.
The following parameters in the smb.conf file sections define a share control or affect access controls.
Before using any of the following options, please refer to the man page for smb.conf.
User- and group-based controls can prove quite useful. In some situations it is distinctly desirable to force all file system operations as if a single user were doing so. The use of the force user and force group behavior will achieve this. In other situations it may be necessary to use a paranoia level of control to ensure that only particular authorized persons will be able to access a share or its contents. Here the use of the valid users or the invalid users parameter may be useful.
As always, it is highly advisable to use the easiest to maintain and the least ambiguous method for controlling access. Remember, when you leave the scene, someone else will need to provide assistance, and if he or she finds too great a mess or does not understand what you have done, there is risk of Samba being removed and an alternative solution being adopted.
User and Group Based Controls enumerates these controls.
Table 16.2. User- and Group-Based Controls
| Control Parameter | Description, Action, Notes |
|---|---|
| admin users | List of users who will be granted administrative privileges on the share. They will do all file operations as the superuser (root). Users in this list will be able to do anything they like on the share, irrespective of file permissions. |
| force group | Specifies a UNIX group name that will be assigned as the default primary group for all users connecting to this service. |
| force user | Specifies a UNIX username that will be assigned as the default user for all users connecting to this service. This is useful for sharing files. Incorrect use can cause security problems. |
| guest ok | If this parameter is set for a service, then no password is required to connect to the service. Privileges will be those of the guest account. |
| invalid users | List of users that should not be allowed to login to this service. |
| only user | Controls whether connections with usernames not in the user list will be allowed. |
| read list | List of users that are given read-only access to a service. Users in this list will not be given write access, no matter what the read-only option is set to. |
| username |
Refer to the |
| valid users | List of users that should be allowed to login to this service. |
| write list | List of users that are given read-write access to a service. |
Directory permission-based controls, if misused, can result in considerable difficulty in diagnosing the causes of misconfiguration. Use them sparingly and carefully. By gradually introducing each, one at a time, undesirable side effects may be detected. In the event of a problem, always comment all of them out and then gradually reintroduce them in a controlled way.
Refer to File and Directory Permission Based Controls for information regarding the parameters that may be used to set file and directory permission-based access controls.
Table 16.3. File and Directory Permission-Based Controls
| Control Parameter | Description, Action, Notes |
|---|---|
| create mask |
Refer to the |
| directory mask | The octal modes used when converting DOS modes to UNIX modes when creating UNIX directories. See also directory security mask. |
| dos filemode | Enabling this parameter allows a user who has write access to the file to modify the permissions on it. |
| force create mode | This parameter specifies a set of UNIX-mode bit permissions that will always be set on a file created by Samba. |
| force directory mode | This parameter specifies a set of UNIX-mode bit permissions that will always be set on a directory created by Samba. |
| force directory security mode | Controls UNIX permission bits modified when a Windows NT client is manipulating UNIX permissions on a directory. |
| force security mode | Controls UNIX permission bits modified when a Windows NT client manipulates UNIX permissions. |
| hide unreadable | Prevents clients from seeing the existence of files that cannot be read. |
| hide unwriteable files | Prevents clients from seeing the existence of files that cannot be written to. Unwritable directories are shown as usual. |
| nt acl support | This parameter controls whether smbd will attempt to map UNIX permissions into Windows NT ACLs. |
| security mask | Controls UNIX permission bits modified when a Windows NT client is manipulating the UNIX permissions on a file. |
The parameter documented in Other Controls are often used by administrators
in ways that create inadvertent barriers to file access. Such are the consequences of not understanding the
full implications of smb.conf file settings.
Table 16.4. Other Controls
| Control Parameter | Description, Action, Notes |
|---|---|
| case sensitive, default case, short preserve case | This means that all file name lookup will be done in a case-sensitive manner. Files will be created with the precise file name Samba received from the MS Windows client. |
| csc policy | Client-side caching policy parallels MS Windows client-side file caching capabilities. |
| dont descend | Allows specifying a comma-delimited list of directories that the server should always show as empty. |
| dos filetime resolution | This option is mainly used as a compatibility option for Visual C++ when used against Samba shares. |
| dos filetimes | DOS and Windows allow users to change file timestamps if they can write to the file. POSIX semantics prevent this. This option allows DOS and Windows behavior. |
| fake oplocks | Oplocks are the way that SMB clients get permission from a server to locally cache file operations. If a server grants an oplock, the client is free to assume that it is the only one accessing the file, and it will aggressively cache file data. |
| hide dot files, hide files, veto files | Note: MS Windows Explorer allows override of files marked as hidden so they will still be visible. |
| read only | If this parameter is yes, then users of a service may not create or modify files in the service's directory. |
| veto files | List of files and directories that are neither visible nor accessible. |
This section deals with how to configure Samba per-share access control restrictions.
By default, Samba sets no restrictions on the share itself. Restrictions on the share itself
can be set on MS Windows NT4/200x/XP shares. This can be an effective way to limit who can
connect to a share. In the absence of specific restrictions, the default setting is to allow
the global user Everyone - Full Control (full control, change and read).
At this time Samba does not provide a tool for configuring access control settings on the share itself the only way to create those settings is to use either the NT4 Server Manager or the Windows 200x Microsoft Management Console (MMC) for Computer Management. There are currently no plans to provide this capability in the Samba command-line tool set.
Samba stores the per-share access control settings in a file called share_info.tdb.
The location of this file on your system will depend on how Samba was compiled. The default location
for Samba's tdb files is under /usr/local/samba/var. If the tdbdump
utility has been compiled and installed on your system, then you can examine the contents of this file
by executing tdbdump share_info.tdb in the directory containing the tdb files.
The best tool for share permissions management is platform-dependent. Choose the best tool for your environment.
The tool you need to manage share permissions on a Samba server from a Windows NT4 Workstation or Server is the NT Server Manager. Server Manager is shipped with Windows NT4 Server products but not with Windows NT4 Workstation. You can obtain the NT Server Manager for MS Windows NT4 Workstation from the Microsoft web site support section.
Procedure 16.2. Instructions
Launch the NT4 Server Manager and click on the Samba server you want to administer. From the menu select , then click on .
Click on the share that you wish to manage and click the Properties tab, then click the Permissions tab. Now you can add or change access control settings as you wish.
On MS Windows NT4/200x/XP system, ACLs on the share itself are set using native tools, usually from File Manager. For example, in Windows 200x, right-click on the shared folder, then select , then click on Permissions. The default Windows NT4/200x permission allows "Everyone" full control on the share.
MS Windows 200x and later versions come with a tool called the Computer Management snap-in for the MMC. This tool is located by clicking on .
Procedure 16.3. Instructions
After launching the MMC with the Computer Management snap-in, click the menu item and select Connect to another computer. If you are not logged onto a domain you will be prompted to enter a domain login user identifier and a password. This will authenticate you to the domain. If you are already logged in with administrative privilege, this step is not offered.
If the Samba server is not shown in the Select Computer box, type in the name of the target Samba server in the field Name:. Now click the on next to System Tools, then on the next to Shared Folders in the left panel.
In the right panel, double-click on the share on which you wish to set access control permissions. Then click the tab Share Permissions. It is now possible to add access control entities to the shared folder. Remember to set what type of access (full control, change, read) you wish to assign for each entry.
Warning
Be careful. If you take away all permissions from the Everyone user without removing
this user, effectively no user will be able to access the share. This is a result of what is known as
ACL precedence. Everyone with no access means that MaryK who is
part of the group Everyone will have no access even if she is given explicit full
control access.
Windows NT clients can use their native security settings dialog box to view and modify the underlying UNIX permissions.
This ability is careful not to compromise the security of the UNIX host on which Samba is running and still obeys all the file permission rules that a Samba administrator can set.
Samba does not attempt to go beyond POSIX ACLs, so the various finer-grained access control options provided in Windows are actually ignored.
Note
All access to UNIX/Linux system files via Samba is controlled by the operating system file access controls. When trying to figure out file access problems, it is vitally important to find the identity of the Windows user as it is presented by Samba at the point of file access. This can best be determined from the Samba log files.
From an NT4/2000/XP client, right-click on any file or directory in a Samba-mounted drive letter
or UNC path. When the menu pops up, click on the Properties entry at the bottom
of the menu. This brings up the file Properties dialog box. Click on the
Security tab and you will see three buttons: ,
, and . The
button will cause either an error message "A requested privilege is not held by the client"
to appear if the user is not the NT administrator, or a dialog intended to allow an administrator
to add auditing requirements to a file if the user is logged on as the NT administrator. This dialog is
nonfunctional with a Samba share at this time, because the only useful button, the
button, will not currently allow a list of users to be seen.
Clicking on the button brings up a dialog box telling you who owns the given file. The owner name will be displayed like this:
SERVER\user (Long name)
SERVER is the NetBIOS name of the Samba server, user
is the username of the UNIX user who owns the file, and (Long name) is the
descriptive string identifying the user (normally found in the GECOS field of the UNIX password database).
Click on the button to remove this dialog.
If the parameter nt acl support is set to false,
the file owner will be shown as the NT user Everyone.
The button will not allow you to change the ownership of this file to yourself (clicking it will display a dialog box complaining that the user as whom you are currently logged onto the NT client cannot be found). The reason for this is that changing the ownership of a file is a privileged operation in UNIX, available only to the root user. Because clicking on this button causes NT to attempt to change the ownership of a file to the current user logged into the NT client, this will not work with Samba at this time.
There is an NT chown command that will work with Samba and allow a user with administrator
privilege connected to a Samba server as root to change the ownership of files on both a local NTFS file system
or remote mounted NTFS or Samba drive. This is available as part of the Seclib NT
security library written by Jeremy Allison of the Samba Team and is downloadable from the main Samba FTP site.
The third button is the button. Clicking on it brings up a dialog box that shows both the permissions and the UNIX owner of the file or directory. The owner is displayed like this:
SERVER\
user
(Long name)
SERVER is the NetBIOS name of the Samba server,
user is the username of the UNIX user who owns the file, and
(Long name) is the descriptive string identifying the user (normally found in the
GECOS field of the UNIX password database).
If the parameter nt acl support is set to false,
the file owner will be shown as the NT user Everyone, and the permissions will be
shown as NT Full Control.
The permissions field is displayed differently for files and directories. Both are discussed next.
The standard UNIX user/group/world triplet and the corresponding read, write,
execute permissions triplets are mapped by Samba into a three-element NT ACL with the
“r”, “w”, and “x” bits mapped into the corresponding NT
permissions. The UNIX world permissions are mapped into the global NT group Everyone, followed
by the list of permissions allowed for the UNIX world. The UNIX owner and group permissions are displayed as an NT
user icon and an NT local group icon, respectively, followed by the list
of permissions allowed for the UNIX user and group.
Because many UNIX permission sets do not map into common NT names such as read,
change, or full control, usually the permissions will be prefixed
by the words Special Access in the NT display list.
But what happens if the file has no permissions allowed for a particular UNIX user group or world component?
In order to allow no permissions to be seen and modified, Samba then overloads the NT
Take Ownership ACL attribute (which has no meaning in UNIX) and reports a component with
no permissions as having the NT O bit set. This was chosen, of course, to make it look
like a zero, meaning zero permissions. More details on the decision behind this action are given below.
Directories on an NT NTFS file system have two different sets of permissions. The first set is the ACL set on the
directory itself, which is usually displayed in the first set of parentheses in the normal RW
NT style. This first set of permissions is created by Samba in exactly the same way as normal file permissions are, described
above, and is displayed in the same way.
The second set of directory permissions has no real meaning in the UNIX permissions world and represents the
inherited permissions that any file created within this directory would inherit.
Samba synthesizes these inherited permissions for NT by returning as an NT ACL the UNIX permission mode that a new file created by Samba on this share would receive.
Modifying file and directory permissions is as simple as changing the displayed permissions in the dialog box and clicking on . However, there are limitations that a user needs to be aware of, and also interactions with the standard Samba permission masks and mapping of DOS attributes that also need to be taken into account.
If the parameter nt acl support is set to false, any attempt to
set security permissions will fail with an "Access Denied" message.
The first thing to note is that the button will not return a list of users in Samba (it will give an error message saying "The remote procedure call failed and did not execute"). This means that you can only manipulate the current user/group/world permissions listed in the dialog box. This actually works quite well because these are the only permissions that UNIX actually has.
If a permission triplet (either user, group, or world) is removed from the list of permissions in the NT
dialog box, then when the button is pressed, it will be applied as no
permissions on the UNIX side. If you view the permissions again, the no
permissions entry will appear as the NT O flag, as described above. This allows
you to add permissions back to a file or directory once you have removed them from a triplet component.
Because UNIX supports only the “r”, “w”, and “x” bits of an NT ACL, if
other NT security attributes such as Delete Access are selected, they will be ignored
when applied on the Samba server.
When setting permissions on a directory, the second set of permissions (in the second set of parentheses) is by default applied to all files within that directory. If this is not what you want, you must uncheck the Replace permissions on existing files checkbox in the NT dialog before clicking on .
If you wish to remove all permissions from a user/group/world component, you may either highlight the
component and click on the button or set the component to only have the special
Take Ownership permission (displayed as O) highlighted.
There are four parameters that control interaction with the standard Samba create mask parameters:
When a user clicks on to apply the permissions, Samba maps the given permissions into a user/group/world r/w/x triplet set, and then checks the changed permissions for a file against the bits set in the security mask parameter. Any bits that were changed that are not set to 1 in this parameter are left alone in the file permissions.
Essentially, zero bits in the security mask may be treated as a set of bits the user is not allowed to change, and one bits are those the user is allowed to change.
If not explicitly set, this parameter defaults to the same value as the create mask parameter. To allow a user to modify all the user/group/world permissions on a file, set this parameter to 0777.
Next Samba checks the changed permissions for a file against the bits set in the force security mode parameter. Any bits that were changed that correspond to bits set to 1 in this parameter are forced to be set.
Essentially, bits set in the force security mode parameter
may be treated as a set of bits that, when modifying security on a file, the user
has always set to be on.
If not explicitly set, this parameter defaults to the same value
as the force create mode parameter.
To allow a user to modify all the user/group/world permissions on a file
with no restrictions, set this parameter to 000. The
security mask and force
security mode parameters are applied to the change
request in that order.
For a directory, Samba performs the same operations as
described above for a file except it uses the parameter
directory security mask instead of security
mask, and force directory security mode
parameter instead of force security mode
.
The directory security mask parameter
by default is set to the same value as the directory mask
parameter and the force directory security
mode parameter by default is set to the same value as
the force directory mode parameter.
In this way Samba enforces the permission restrictions that
an administrator can set on a Samba share, while still allowing users
to modify the permission bits within that restriction.
If you want to set up a share that allows users full control
in modifying the permission bits on their files and directories and
does not force any particular bits to be set on,
then set the following parameters in the smb.conf file in that
share-specific section:
security mask = 0777 |
force security mode = 0 |
directory security mask = 0777 |
force directory security mode = 0 |
Note
Samba maps some of the DOS attribute bits (such as “read-only”) into the UNIX permissions of a file. This means there can be a conflict between the permission bits set via the security dialog and the permission bits set by the file attribute mapping.
If a file has no UNIX read access for the owner, it will show up as “read-only” in the standard file attributes tabbed dialog. Unfortunately, this dialog is the same one that contains the security information in another tab.
What this can mean is that if the owner changes the permissions to allow himself or herself read access using the security dialog, clicks on to get back to the standard attributes tab dialog, and clicks on on that dialog, then NT will set the file permissions back to read-only (as that is what the attributes still say in the dialog). This means that after setting permissions and clicking on to get back to the attributes dialog, you should always press rather than to ensure that your changes are not overridden.
Windows administrators are familiar with simple ACL controls, and they typically consider that UNIX user/group/other (ugo) permissions are inadequate and not sufficiently fine-grained.
Competing SMB implementations differ in how they handle Windows ACLs. Samba handles Windows ACLs from the perspective of UNIX file system administration and thus adopts the limitations of POSIX ACLs. Therefore, where POSIX ACLs lack a capability of the Windows NT/200X ACLs, the POSIX semantics and limitations are imposed on the Windows administrator.
POSIX ACLs present an interesting challenge to the UNIX administrator and therefore force a compromise to be applied to Windows ACLs administration. POSIX ACLs are not covered by an official standard; rather, the latest standard is a draft standard 1003.1e revision 17. This is the POSIX document on which the Samba implementation has been implemented.
UNIX vendors differ in the manner in which POSIX ACLs are implemented. There are a number of Linux file systems that support ACLs. Samba has to provide a way to make transparent all the differences between the various implementations of POSIX ACLs. The pressure for ACLs support in Samba has noticeably increased the pressure to standardize ACLs support in the UNIX world.
Samba has to deal with the complicated matter of handling the challenge of the Windows ACL that implements inheritance, a concept not anticipated by POSIX ACLs as implemented in UNIX file systems. Samba provides support for masks that permit normal ugo and ACLs functionality to be overrided. This further complicates the way in which Windows ACLs must be implemented.
In examining POSIX ACLs we must consider the manner in which they operate for both files and directories. File ACLs have the following significance:
# file: testfile <- the file name # owner: jeremy <-- the file owner # group: users <-- the POSIX group owner user::rwx <-- perms for the file owner (user) user:tpot:r-x <-- perms for the additional user `tpot' group::r-- <-- perms for the file group owner (group) group:engrs:r-- <-- perms for the additonal group `engineers' mask:rwx <-- the mask that is `ANDed' with groups other::--- <-- perms applied to everyone else (other)
Directory ACLs have the following signficance:
# file: testdir <-- the directory name # owner: jeremy <-- the directory owner # group: jeremy <-- the POSIX group owner user::rwx <-- directory perms for owner (user) group::rwx <-- directory perms for owning group (group) mask::rwx <-- the mask that is `ANDed' with group perms other:r-x <-- perms applied to everyone else (other) default:user::rwx <-- inherited owner perms default:user:tpot:rwx <-- inherited extra perms for user `tpot' default:group::r-x <-- inherited group perms default:mask:rwx <-- inherited default mask default:other:--- <-- inherited permissions for everyone (other)
Microsoft Windows NT4/200X ACLs must of necessity be mapped to POSIX ACLs.
The mappings for file permissions are shown in How
Windows File ACLs Map to UNIX POSIX File ACLs.
The # character means this flag is set only when the Windows administrator
sets the Full Control flag on the file.
Table 16.5. How Windows File ACLs Map to UNIX POSIX File ACLs
| Windows ACE | File Attribute Flag |
|---|---|
Full Control | # |
Traverse Folder/Execute File | x |
List Folder/Read Data | r |
Read Attributes | r |
Read Extended Attribures | r |
Create Files/Write Data | w |
Create Folders/Append Data | w |
Write Attributes | w |
Write Extended Attributes | w |
Delete Subfolders and Files | w |
Delete | # |
Read Permissions | all |
Change Permissions | # |
Take Ownership | # |
As can be seen from the mapping table, there is no one-to-one mapping capability, and therefore Samba must make a logical mapping that will permit Windows to operate more-or-less the way that is intended by the administrator.
In general the mapping of UNIX POSIX user/group/other permissions will be mapped to Windows ACLs. This has precedence over the creation of POSIX ACLs. POSIX ACLs are necessary to establish access controls for users and groups other than the user and group that own the file or directory.
The UNIX administrator can set any directory permission from within the UNIX environment. The Windows administrator is more restricted in that it is not possible from within Windows Explorer to remove read permission for the file owner.
Interesting things happen in the mapping of UNIX POSIX directory permissions and UNIX POSIX ACLs to Windows ACEs (Access Control Entries, the discrete components of an ACL) are mapped to Windows directory ACLs.
Directory permissions function in much the same way as shown for file permissions, but there are some notable exceptions and a few peculiarities that the astute administrator will want to take into account in the setting up of directory permissions.
File, directory, and share access problems are common topics on the mailing list. The following are examples recently taken from the mailing list.
The following complaint has frequently been voiced on the Samba mailing list:
“
We are facing some troubles with file/directory permissions. I can log on the domain as admin user (root),
and there's a public share on which everyone needs to have permission to create/modify files, but only
root can change the file, no one else can. We need to constantly go to the server to
chgrp -R users * and chown -R nobody * to allow
other users to change the file.
”
Here is one way the problem can be solved:
Go to the top of the directory that is shared.
Set the ownership to whatever public user and group you want
$find `directory_name' -type d -exec chown user:group {}\;$find `directory_name' -type d -exec chmod 2775 {}\;$find `directory_name' -type f -exec chmod 0775 {}\;$find `directory_name' -type f -exec chown user:group {}\;Note
The above will set the
SGID biton all directories. Read your UNIX/Linux man page on what that does. This ensures that all files and directories that are created in the directory tree will be owned by the current user and will be owned by the group that owns the directory in which it is created.Directory is
/foodbar:$chown jack:engr /foodbarNote
This is the same as doing:
$chown jack /foodbar$chgrp engr /foodbarNow type:
$chmod 2775 /foodbar$ls -al /foodbar/..You should see:
drwxrwsr-x 2 jack engr 48 2003-02-04 09:55 foodbar
Now type:
$su - jill$cd /foodbar$touch Afile$ls -alYou should see that the file
Afilecreated by Jill will have ownership and permissions of Jack, as follows:-rw-r--r-- 1 jill engr 0 2007-01-18 19:41 Afile
If the user that must have write permission in the directory is not a member of the group engr set in the
smb.confentry for the share:force group = engr
When you have a user in admin users, Samba will always do file operations for this user as root, even if force user has been set.
Question: “When user B saves a word document that is owned by user A, the updated file is now owned by user B. Why is Samba doing this? How do I fix this?”
Answer: Word does the following when you modify/change a Word document: MS Word creates a new document with a temporary name. Word then closes the old document and deletes it, then renames the new document to the original document name. There is no mechanism by which Samba can in any way know that the new document really should be owned by the owners of the original file. Samba has no way of knowing that the file will be renamed by MS Word. As far as Samba is able to tell, the file that gets created is a new file, not one that the application (Word) is updating.
There is a workaround to solve the permissions problem. It involves understanding how you can manage file
system behavior from within the smb.conf file, as well as understanding how UNIX file systems work. Set on the directory
in which you are changing Word documents: chmod g+s `directory_name'. This ensures that all files will
be created with the group that owns the directory. In smb.conf share declaration section set:
force create mode = 0660 |
force directory mode = 0770 |
These two settings will ensure that all directories and files that get created in the share will be readable/writable by the owner and group set on the directory itself.